InfoSight for Servers
By Michael Gosselin / November 19, 2019 / HPEinfosightpredictive analyticsproliantsynergy
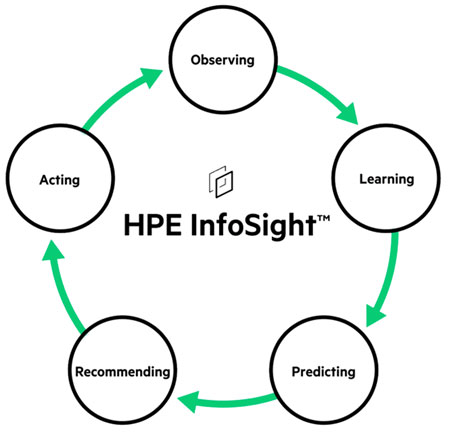
HPE InfoSight With the purchase of Nimble, HPE gained a great storage platform. It also gained the valuable asset of InfoSight. InfoSight is an AI-driven predictive analytics tool which enables customers to gain higher efficiency and reliability with smarter, easy to manage infrastructure. HPE InfoSight automatically predicts and resolves 86 percent of issues before a […]
READ MORE
Ransomware 101
By Adam Gosselin / November 13, 2019 / backupmalwareransomwarevirus
Ransomware In May 2017, the National Health Service of England and Scotland was hit with the largest ransomware attack at that time. The attack affected an estimated 200,000 computers across 150 countries. The estimated economic loss ranges from hundreds of millions to four billion dollars. This attack, dubbed the WannaCry ransomware attack, catapulted network […]
READ MORE
Ransomware Focus: Local Governments, Schools and Healthcare
By Zunesis / November 7, 2019 / governementransomwareransomware attacksschools
New Ransomware Focus Ransomware has a new focus. Recent studies and surveys report that ransomware attacks have sky rocketed against government agencies, public healthcare providers and schools in the first nine months of 2019. A report published by Emsisoft noted that at least 68 state, county and municipal entities have been affected by ransomware attacks this […]
READ MORESearch
Blog Categories
Related Resources
Archives
- April 2025
- March 2025
- February 2025
- January 2025
- October 2024
- September 2024
- August 2024
- July 2024
- June 2024
- May 2024
- April 2024
- March 2024
- January 2024
- October 2023
- September 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- March 2023
- February 2023
- January 2023
- October 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
- September 2021
- August 2021
- July 2021
- June 2021
- May 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- August 2020
- July 2020
- June 2020
- May 2020
- April 2020
- March 2020
- February 2020
- January 2020
- December 2019
- November 2019
- October 2019
- September 2019
- August 2019
- July 2019
- June 2019
- May 2019
- April 2019
- March 2019
- February 2019
- January 2019
- December 2018
- November 2018
- October 2018
- September 2018
- August 2018
- July 2018
- June 2018
- May 2018
- April 2018
- March 2018
- February 2018
- January 2018
- December 2017
- November 2017
- October 2017
- September 2017
- August 2017
- July 2017
- June 2017
- May 2017
- April 2017
- March 2017
- February 2017
- January 2017
- December 2016
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- May 2016
- March 2016
- February 2016
- January 2016
- December 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2014
- February 2013




