Username + Password != 2FA

What are MFA, 2FA, and why do we need them?

“Something you know, something you have, something you are.” This is stated by Multi-Factor Authentication enthusiasts all over the web. They are ways of identifying yourself for the purpose of gaining access to a system. Examples of these would be your username/password combination, a OTP (One Time Password) sent be SMS or authenticator app, and biometrics. 2FA is of course a subset of MFA. It uses two factors to authenticate your logon. AND NO, USERNAME + PASSWORD ARE NOT TWO FACTORS.
Compared to single factor authentication, MFA ensures that your accounts are much better protected. “99.9% less likely to be compromised” is found on Microsoft based on their records of 99.9% of compromised accounts not using MFA. This was stated by Alex Weinert, Director of Identity Security at Microsoft at a recent cyber security conference.

Perhaps even more disturbing is that there is ONLY AN 11% MFA ADOPTION RATE AMONG ENTERPRISE CLOUD USERS. It’s not like we keep important data in our business emails. We also don’t use these same emails as recovery addresses for other business related online accounts. Joking aside, we are almost asking for security breaches.
Why aren’t you using Multi-factor Authentication?
We live in times where ransomware, social engineering, and other cyber attacks are on the rise. By not utilizing multi-factor authentication, you are doing the equivalent of using 1-2-3-4-5 as your combination on your luggage. Something almost as bad is re-using the same couple of passwords everywhere. Your password expired? Just update it from SecurePW1! to SecurePW2@ and it will meet complexity requirements and be super secure, right?
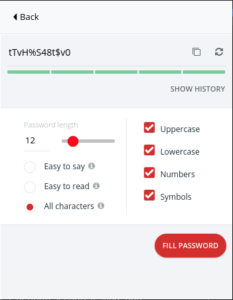
The practical issue with using very complicated passwords is that they are very difficult to remember by design. This is where a password manager is very helpful. You don’t want to be the person with a bunch of sticky notes on your monitor with login credentials written on them.

You can generate very secure passwords as seen in the LastPass example below, and store them in a vault.
Combined with a complicated password, using MFA will make it much harder for bad actors to impersonate you. Most online services these days give the option of enabling multi-factor authentication. Examples are business apps like Office 365, Google Apps/Gmail, your work’s VPN application, and even personal apps like your bank, Amazon, or Facebook offer this. Your password manager is also a very good candidate to enable MFA.
How can you get started?
First, you need another factor for authentication. Hardware devices such as RSA SecureID or Yubico’s YubiKey are good choices if you really want to take things seriously. You can also just use an app. Popular apps such as Google Authenticator, Microsoft Authenticator, Authy, and Lastpass Authenticator are all good examples.
Next, head over to your favorite application and log in. Usually in the same place in the settings area where you would change a password, there should be an option to enable 2FA/MFA/2-step verification/etc. While you’re at it, you should probably change your password if it isn’t complex or you haven’t done so in a while.
Just follow the instructions to enable MFA. This will vary slightly depending on application. In general, you’ll select your authenticator app or hardware key when prompted. If using an authenticator app, you will need to scan a QR code to add that account. Once you complete the setup, enjoy knowing that your security posture has been greatly improved.
Need help enabling MFA on your business applications such as Office 365 or your VPN client? Contact us today. Our friendly Zunesis engineers are here to help!
Categories
Search
Blog Categories
Related Resources
Archives
- July 2024
- June 2024
- May 2024
- April 2024
- March 2024
- January 2024
- October 2023
- September 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- March 2023
- February 2023
- January 2023
- October 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
- September 2021
- August 2021
- July 2021
- June 2021
- May 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- August 2020
- July 2020
- June 2020
- May 2020
- April 2020
- March 2020
- February 2020
- January 2020
- December 2019
- November 2019
- October 2019
- September 2019
- August 2019
- July 2019
- June 2019
- May 2019
- April 2019
- March 2019
- February 2019
- January 2019
- December 2018
- November 2018
- October 2018
- September 2018
- August 2018
- July 2018
- June 2018
- May 2018
- April 2018
- March 2018
- February 2018
- January 2018
- December 2017
- November 2017
- October 2017
- September 2017
- August 2017
- July 2017
- June 2017
- May 2017
- April 2017
- March 2017
- February 2017
- January 2017
- December 2016
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- May 2016
- March 2016
- February 2016
- January 2016
- December 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2014
- February 2013




